Your physical business security is important component of how secure your overall business is. Right now, the hot word is cybersecurity. By neglecting physical security for your business, you are shooting yourself in the foot.
Physical business security does not involve a room with elite ex-military personnel training in “all or nothing ninja mode”. In fact, despite the narrative that led to the false impression from movies Sneakers and Hackers, you likely will not be infiltrated by some group of skilled former military personnel and programmers, nor from semi-attractive neo-punk teenagers.
Instead, you are more likely to be hacked, or cracked, at your business’s physical location by a normal looking person. The TL;DR for this article is that people trust badges, people will hold open doors for hard workers and they rarely question you if they see you with others in the company.
In fact, your next infiltration likely will be from this guy…

Or could be from this woman…

Your business can, and likely could, be physically targeted. It probably won’t be from a team of ninja coders and programmers. And when you are targeted by a group of gifted hackers, the outcome is even worse than you could expect.
Who and how of physical security hacking
You might need some examples of people that could get into your business from poor physical security?
Your next infiltration could be from a disgruntled employee sitting along in the office one day. Or from an over-friendly delivery person. Or from a person asking to use the restroom with a baby in-hand.
So, what should you look out for as you walk around the office? What specifics should your employees question and investigate?
What follows is an overview of some issues that your business might need to plug immediately. Also, we will look at how to solve these issues. You should walk away with a better understanding of basic physical security in a business environment, and how to cure those ills.
DOORS, LOCKS AND KEYS … OH MY!!!
Bad security shows possible attackers your weaknesses. Terrible security leaves the keys in the locks. The worst security doesn’t care either way.
How many times have you been angry that you ‘wasted’ time having to unlocked something, then relock it – only to leave it unlocked?
How many times have your employees?
And worse, how many times have you done something putting your brand at risk with lax security?
Need an example?
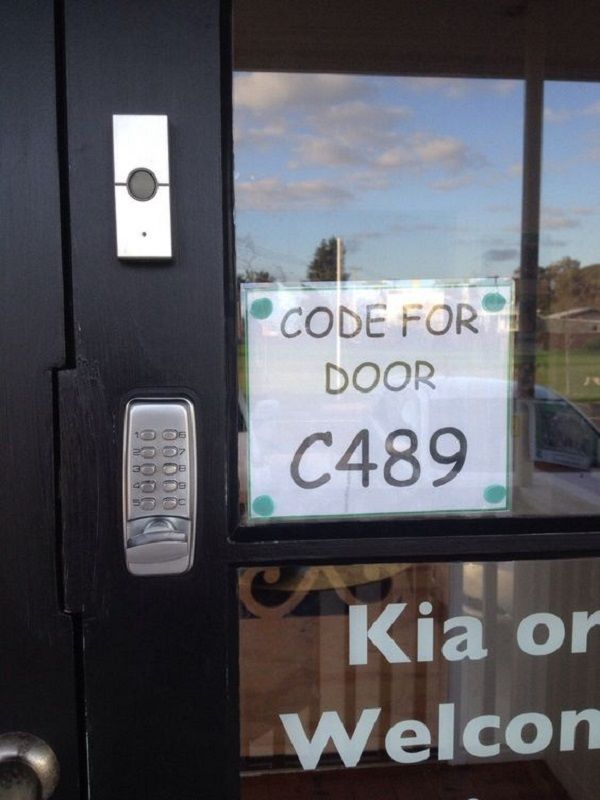
… or this …

… possibly even..this???

How can you fix it?
Locks and keys work, but they must be used properly.
Look, everything and anything can use a lock to make it more secure.
What physical deterrents can be used for your business?
Computers and laptops can use security locks to physically halt people from stealing them, and then accessing them. Secure computer locks and laptop locks can help to handle this for you.
To take the idea of locks and keys a step further, you can also use secure USB locks and port locks. While your mileage will vary with these devices, we are attempting to deter and slow the assault, because you can’t always stop them from happening.
If you charge items in external locations (which we would NEVER advise), you could use a product like this security device. What we recommend instead of USB charging protection is to buy a good portable charger if having the need for recharging your devices is necessary.
LOGOUT FROM APPLICATIONS AND DEVICES
When you physically step away from the computer or laptop, log out. Think of you logging into and out of your PC as your physical presence being there. When you leave, it should leave as well.
I know logging in and out of a computer can be time-consuming, especially during really busy days. However, the simple act of logging out creates an additional step someone trying to infiltrate your system needs to go through.
If you need speed, keep the device physically with you if possible. Or, you can use a bio-metric login to facilitate faster logins.
I’ll never forget going to the neurologist with my wife. We were left in the room some ten minutes with a laptop they used for office visits. The laptop was logged on, WiFi open, with us for ten minutes. This would’ve been more than enough time to install and execute malware or a virus, plug in a USB drive and start downloading, or access other parts of their system.
Things were VERY different at my dentist’s office. At my dentist’s office, whenever the dentist or assistant would leave the room, they logout. The case for the PC is held behind a locked door. And, their PC login is a different password than their network login, and the medical network (UPMC) login.
Leaving a login open, with an open device in a business, is quite literally like leaving the cookies and the cookie jar out and in the open. If someone wants something malicious done, then you just handed them the opportunity to do just that.
QUESTION EVERYONE, ALL THE TIME
People need to be less trusting whenever someone enters their business. Some people are there to work, or to buy, or to browse. Others can be there to surveil, or to occupy, or to steal.
If you use badges to move from area to area, question the person and the badge. If you see someone unfamiliar, question their being there.
My daughter recently did shadowing at a school. When she arrived, she was questioned by the guard. He never asked to examine her purse, never asked to see an ID either. He passed this security check onto the office. The office, assuming she was allowed to be there, never asked to check either.
Breakdowns like this happen every, single day. Assumption is mother of all messes.
Instead, you should always stop, ask and then verify – that simple.
SMOKING CAN GET YOU HACKED
Smoke areas are sometimes flimsy locations of security. This isn’t an anti-smoking riff; its a truth.
Let me lay this one out…
Imagine you want to get into a locked door. This particular door exists adjacent to a smoke break area outside. So, you sit, smoking a cigarette, with a fake badge, but one matching some company colors and your picture on it. During the smoke break, people come out, one by one and then two by four.
As the smoke break ends, you give one more drag on your cigarette. You look at your watch for no reason, and then walk, in-file, with the group.
Congratulations! You’ve just broken into a security building with nothing more than a cigarette and a look at your watch!
Like any security point requiring pass-codes or badges, there should be a single check-in per person. Basically, each person opens the door, walks through and closes the door. Now you know exactly the personnel in the building. And, because each person had to use a badge or code to enter, you have eliminated ‘pack hacking’ from occurring.
The above method of deterring pack hacking might not be effective. However, now that you know about the method, you can correct it.
VERIFY ALL CONTRACTORS, VISITORS AND NON-EMPLOYEES
As soon as a person enters your business, make contact. Be courteous, but kind. However, do not be trusting.
Anyone can have malicious goals in mind. These could be as simple as placing something on a cork-board, to using your phone, to actually hijacking your whole system.
A good first step is to limit both physical and digital access to these workers. A recent hack on Target’s system wasn’t on their system itself; it was on the HVAC company that the company hired. Because Target granted access and rights that were everywhere, a hacker targeting that company, now had access to Target as well.
The next step is to verify anyone and everyone coming into the business.
You should be looking up numbers and verifying visits. You should be stopping visitors and checking credentials. You are the first and last line of your company’s physical security.
Wrapping up the physical security talk…
Your business’s physical security is one part of your overall security need. By physically removing as many possible points of intrusions into your company, you are making your customers safer, your data safer and preventing future lawsuits and fines.
Now that you started physically securing your business, let us help you secure your business data for free!