I hated my first day of school. I’m sure you had a similar feeling.
Look, there were a lot of firsts on that day. It was the first time I was riding the bus alone. It was the first time I would be going to “school”. It was the first time I would be around a lot of kids having their own ‘first days’ of school.
After weeks, if not months, of being told how it was, my assumptions were simple: something bad might happen, but it’ll be ok.
I didn’t know what was going to happen while waiting for the bus. I didn’t know what would happen during the day. I didn’t know what would happen by the end of the day.
I was afraid. I knew what I needed to do, but decided to just assume things would be fine and not plan, not think and simply follow the crowd.
…and that ended with me getting off of the bus at the wrong school.
Seriously…

My bus went to one school, and then went to a second. I was supposed to go to the second school. That day, I didn’t. And I was miserable. Being nervous, being stressed out, being scared of things was one thing, but this was something else.
The second day was different. It was my second day – my real ‘first’ day. But this time, I had something I didn’t have in the past. I had a checklist of things to do, and things to not do. I had the ability to understand the problems and to get past them.
What does this have to do with small business security?
I’m sure your assumptions have benefited you in the past. More likely than not, it was only an assumption based on fact, experts and experience that panned out in a positive way. Am I right?
Small business owners like you are an awesome breed. They are hard-working, connected people who plan and execute constantly.
However, they also have a few problems with business security. Sometimes, you might have gotten off at the wrong stop and started to believe some of the wrong reasons to not build your security in your brand. Some things like:
- We’re too small to worry about hackers
- No one wants our information (it’s boring, not valuable, etc)
- Extra security is too expensive
Are any of these you?
It’s not a problem if that is true. We’re going to make your business security a lot more simple, more affordable (try free) and faster to implement. In fact, by the time you finish this article and grab your free small business security checklist, your 2018 will be nothing like my first day at school.
Threat modeling basics
All of your security needs in business should start with threat modeling.
Threat modeling is the process of reviewing and analyzing your security – where are the holes and who are they coming from? With this review, we can find out where the security issues are to fix them fully.
Why am I bringing this up to you?
Threat modeling directly relates to your small business security.
Let me explain…
In businesses, there are quite a few parts to your threat modeling. Every employee needs analyzed. Every type of customer (physical and via digital means) needs to be reviewed. All physical parts of the business need to be reviewed. And all the digital business security needs to be looked at. Plus you need to look at the physical layout of the business, the partners and contractors that you work with and more.
Generally, threat modeling starts with asking, and answering, the following. These answers will start your thinking and decision-making to get your business in a secure position.
- What do you need to protect?
- Who do you want to protect if from?
- How likely is it that you need to protect it?
- How bad are the consequences if you fail?
- How much trouble are you willing to go through in order to try to prevent those?
While this is a serious subject, you can also gamify this process. Role-play various people that interact with the business. Role-play various people that might actively attempt break-ins, hacks and phishing campaigns. What happens? What can happen?
Below, we take this a bit further as we look at your business. You should have a checklist, step by step and item by item, of things to consider. Like most security items, some of these parts might seem insignificant – they are until someone hacks them.
One word about this small business security guide…
Look, security is a serious thing. This guide is meant to be a catalyst for your change. To take small steps (and some big), so that you business gets more secure in 2018.
However, one guide, on one website, just isn’t enough. After all, intrusions and hacking costs small businesses on average about $3.6 million dollars per year, per incident. That possible outcome is worth a lot more than a 5 minute read.
This guide is meant to get you to take action, to start making some changes and then to hire a professional to get the right training, tools and procedures in place for your brand. When you are ready to start the walk down the road of ‘better business security’, there are plenty of resources to fully tune your security needs with your business.
And, if you want to add to this, be sure to download the small business security checklist. You get free, printable checklists for yourself and your employees.
Securing your offline business issues
While PerfectShare is an online tools for file sharing, not every business exists in the digital world alone. You will need physical protection as well. You will need physical safety.
Above, we looked a little at threat modeling. We looked at what we should be asking about – the who, where, when and hows. Now, we start putting into place the solutions to some of those thoughts.
But, first, a question…
If there were a golden lamp with a genie with three wishes placed inside of your offices, right now…how would you get to it? And how would you prevent yourself from getting it? Your business is like that. It can give you the security and comfort of income. However, when not protected, it could see you lose everything.
Basics for locks, doors and operation
Locks and keys are the symbol of security. Literally, look up ‘security’ in Google Images and you’ll see!
The first step we need to address are the physical locks at your office space. Without a barrier between your sensitive data and the outside world, you are open to any and every attacker out there. Then we move onto containers, other entrances and suppression and removal systems for things like fire and flood.
Doors should be in working condition, with locks installed. All exterior doors should have multiple locks installed and working – one for operating hours, and the rest for non-operational hours. Interior doors only need one lock to be considered secure. However, if sensitive data like financials, healthcare, legal or other valuable resources are stored behind the door(s), using multiple locks might be required for compliance standards.

Windows are a security issue that is easy to address. First, make sure that they are in working order – they slide up, the slide down, they slide side to side if needed and are not broken. Make sure all locks are operational. If a security system is installed, test this monthly, at least.
Computers should physically be secured with rope or wire locks and port locks. Rope locks work much like bicycle locks by not allowing the computer to be physically moved or removed, nor opened. Port locks prevent people from accessing your computer terminals directly without the need to login.
Drawers and desks should be locked. The tops of your workstation and desk should not contain sensitive materials when you are not using them. These can include passwords, financial data, medical data and more.
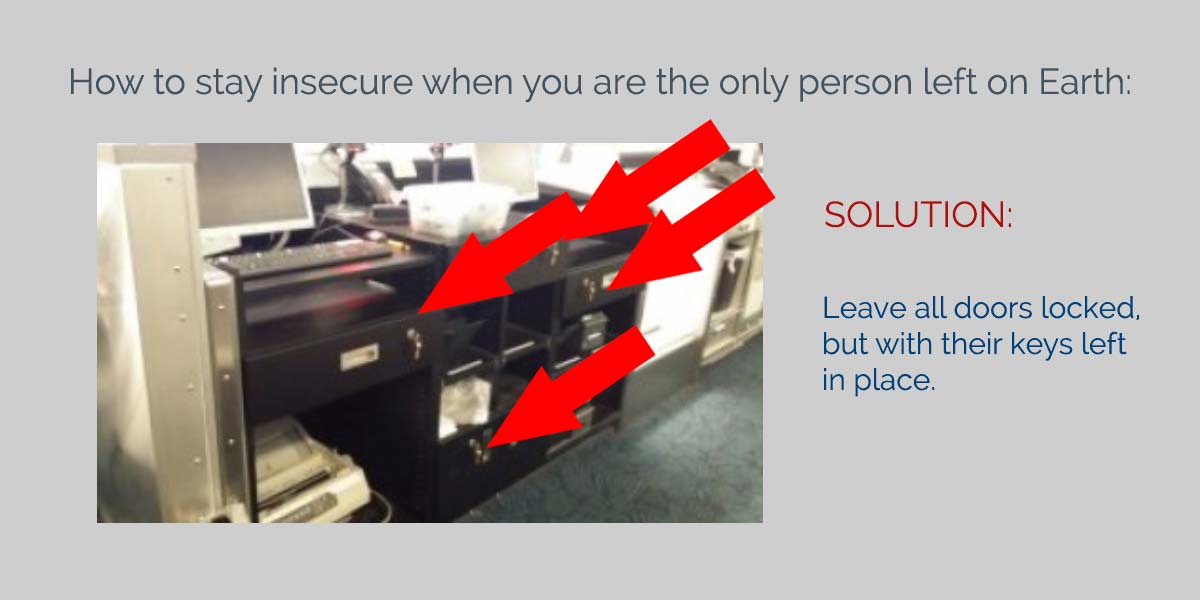
File cabinets need to be locked, without their keys left in the cylinder. Some businesses I’ve seen leave the keys to the locked file cabinets in the file cabinets. This is equivalent to a bank leaving the safe combination ‘stickied’ on it.
Lighting makes your business more secure
Light is a deterrent. Plain and simple.
Using lighting at your office will make your business more secure from day one. There can be some debate about the type of light, color and intensity – however, LED lights are the clearest and most cost-effective.
Use “always-on” lighting for any entrance. Every doorway that allows for people to come in or go out must work and be installed.
Use motion lights for points of entry (not just doors). Can someone possibly gain access from a window? Are there basement transoms or windows? Is there a sliding door or fence that allows someone to gain access? Basically, you need motion sensor lights for places that allows someone to gain access to something (not just inside of your building) that can hinder, harm or hack your company.
Use the correct interior lighting during and after work hours. Lighting should spotlight areas that need additional security. If using a security camera system, you should direct light at correct levels. Quickly replacing bulbs with correct lighting is essential.
Make sure electronic & mechanical security is working
You might be like me – set it and forget it. I buy something awesome, plug it into the wall and then just forget about its maintenance, because it just ‘works’.
But everything electronic needs to be updated. These items need to be maintained – especially when it comes to your business.
All key-less doors and entry points need tested. Test fobs and the reporting software. It should also be mentioned that the default access passwords and fobs need changed out.
Your gates, fencing and walls need to be tested weekly. You should be testing their working condition, as well as the method used to enter these areas; security cards, passcode keypads, fobs, etc.

Your company’s security cameras should be tested. There are two main areas to test and review for security cameras – positioning and broadcast. If the security camera mounts are weak, you will loose the viewed angle. If the motor that controls its movement is broken or worn, then you will lose that activity as well. Likewise, without a working signal being broadcast into the system, installing the cameras doesn’t matter.
Protection, prevention and suppression systems
Every system needs protected from elements. If you have something flammable (wood, paper, etc), you need fire suppression and protection. If you have ANY possibility of water entering the building from weather or fire suppression or otherwise, you need flood suppression. If you use electricity, then you need electric loss prevention.
Controlling the environment inside of the building is a necessity.
Fire suppression starts with prevention, them the ability to halt its progress. All rooms should have smoke detectors. Fire extinguishers should be fully charged and inspected. Fire escape routes should be posted in easily seen and read areas.
Flooding doesn’t mean floating – it means water that is uncontrolled. Proper drains and spouts (inside and out) should be operating correctly and clean. There should also be a means of elevating any and all electric items off of the ground.
Electricity loss prevention doesn’t mean the lights are out. Use surge protectors to prevent full losses of power. Make sure your electric system is up-to-date and monitored. You will also need to know what happens to locked doors and gates whenever the electricity goes out; someone might be able to simply cut the power and enter your building to steal.
Train people to use security measures correctly
Training is likely your best security cost-to-time method of securing your business in this whole guide. The smarter your employees are, the better they will be at preventing, detailing, notifying and stopping security hacks.
When your employees can identify issues, things can be fixed. This is best done by building and discussing security policies. Training is essential in spotting and stopping security issues. Even something as simple as an employee holding open a door for a delivery person can have an impact.

You need to use an escalation procedure for your employees. Do they notify you? The police? Your IT department?
“Be polite, but never trust.” If you see someone you don’t recognize in your office, approach, ask and verify their details. If you see someone working with an HVAC, electrician, plumber, etc., and they are not presenting security badges or details, confront them. If someone calls into the office and then shows up representing another business, one phone call will verify their claims.
Digital security for your business
Today businesses are heavily connected to the internet – and not just via a computer. Businesses do business via cellphones as well. Smartphones are mobile office-spaces. And because of these things, it makes sense to also make these hotspots of business as secure as possible.
The biggest step in keeping your devices secure is to keep them constantly updated. Security updates and patches are intended to make your device or software more secure after there is an issue found. Without these, your device is a sitting duck to malicious and accidental issues.
Unattended devices are also a major security hole for companies. Never walk away from a computer terminal that is on, unless it is physically secured (lock, remote, etc), and secured via some digital means like a password or login screen. Likewise, don’t leave a laptop, phone or tablet unattended in a public setting.
But, there are more. Follow each of these, step by step, and you will be on a smooth ride towards more safe business activities this year.
Computers and terminals
It doesn’t matter the industry, a computer is the window into your business data. Healthcare, legal, financial, academic, industrial…they all use computers and terminals to handle business.
Use strong(er) passwords for login needs. It goes without saying that today’s passwords are just an insecure as passwords in the past. We still use ‘password123’, ‘123456’ and ‘qwerty’ as passwords for our systems – you can do better.

Use a password manager for storage and for random generation. Stronger passwords mean more difficult to guess – and remember. Because of this, using a password manager is recommended. The extension of these useful pieces of security technology is that most, if not all, have some form of random password generator.
Use 2-factor authentication on those devices. What makes you…you? A name? Can anyone else have the same name? Can someone use your name? Of course! And the same goes for logins. However, when you mix in a physical key or an SMS sent to your mobile device, or one sent to a different email, you then better authenticate yourself as the real person.
Always logoff, sign-off, etc., when you walk away. Let me be clear here – not everyone is looking to hack you. However, based on compliance needs, the sensitive nature of the data and a mountain of other factors, simply logging out when you leave a computer is a smart action.
Never browse from social networks and email links. Employees using computers or other devices for work purposes should never follow links. You open an email, it looks legitimate from a board member or manager, a supplier or someone else…should you click it? 9999 times out of 9999 you shouldn’t.
Keep up-to-date with all tools and applications on the computer. As mentioned previously, unpatched versions of software have security holes are easily plugged up – but are still insecure.
Run anti-malware and anti-virus programs. Don’t make the mistake of thinking because it hasn’t happened, it won’t. Run these programs for extra layers of protection.
Use USB and port locks for extra physical protection of computers. Did you know it takes less than 2 seconds to hijack a computer? Think about it…throw a configured USB drive into an open port and you are good to go. You can deploy malware, hijack-ware, viruses and even listening payloads. These are also fairly affordable at $25-$40 for a starter kit for 4 or 5 computers.
Securing your mobile business devices
They are small. They are powerful. And for some, they are life.
Your smartphone is attached to you. It is how you communicate. It is your ’email client’. It is how you seek and digest news. It is how you trade opinion, how you look up fact and how you build your world.
This power, comes with the need to secure it.
Imagine if your text, your Facebook login and your email are all open. And then, a competitor, a disgruntled former employee or just the general public sees it all. What damage can be done?
This possibility, and all of its brothers and sisters, are the reason that you need to secure it.

Use advanced logins and strong passwords. Some phones allow for passwords. Some allow for facial logins. Others allow you to use shapes, movements and more. If you use a non-action login, then make sure to use strong(er) passwords to be even more secure. Remember, strong passwords work!
Never, ever use open WiFi. This. 100%. Now read it again! You are out and about on your business device. There is open WiFi and your network is down. Do you use it? NO!
Never leave any device unattended. Any unattended device is ripe for the pickin’.
Secure your area before login, and while working on sensitive data. Look around. Who is watching you? Is anyone? Is anyone on their phone around you? Are they recording what your login is? Are they recording what you are reading, writing, reviewing? Secure your area when dealing with data.
Keep all devices and apps up-to-date at all times. Run updates. Don’t skip a security update…ever.
Never let anyone use, view or touch your devices. If you don’t want someone to steal your device, don’t welcome the chance to hand it over to them. I can get anyone’s phone number by simply asking to use their phone, and calling myself. In less than 30 seconds I can change their password. In far less than 5 minutes I can pull everything off of a device.
Use physical locks (like cable locks). Lock down devices with passwords, then lock them down physically.
Use USB and DIM locks. Using USB and DIM locks and keys, you prevent another possibly point on your device.
Final notes on cyber security, physical security and other business issues
Securing your small business might seem overwhelming. In 2017, we were constantly aware of cyber security threats, Russian hacking, US hacking, malware and so much more. Now that we are in 2018, you will hear more. And it is overwhelming.
But you can get started…
Using the areas we talked about today, and some of the solutions, you now have the basic knowledge you need to start securing your business today. Not every hack or intrusion will come from a rogue email, or a forced database attack. It might come from the wrong person entering the building. It could come from a former employee.
Even if you’ve given time to a specific security element, there is always another way to become more secure – and risk security. As time moves on, your business, whether you know it or not, can be a target of a security attack.
The best way to mitigate it? The best way to neutralize it? The best way to prevent the next attack?
With knowledge, and with action.