When my son was 5, he started playing baseball. Ok, so it was T-ball, but it was still baseball to him.
Over the years, he developed more and more. He matched his peers at certain positions, and excelled at others. He hit harder, threw faster and caught better as the seasons went on.
As his 6th season went on, he ran into an issue that his whole team experienced. Like a rash at a week-long camp in the woods, his whole team was crushed by one team and one pitcher. In fact, we heard that every team in his youth baseball league was having the same issue.
What was the problem?
If you ain’t got focus, you ain’t got nothing
The problem was focus.
During each pitch, the second baseman would nearly sprint up behind the pitcher. Or, during another part of the game, the shortstop and the second baseman would both make a massive shift towards third base. Or another time, the catcher would come to a standing position and would run the ball back to the pitcher after the slap of a “STRIKE!” was called.
Focus!
As we started to discuss this problem team, I started to explain what the issue was. My son’s swing was fast and hard. He would dig in and have great form before the pitch. But when those infielders moved, it all fell apart.
After some discussion, we focused in on three pieces to keep in mind during a pitch. First, we agreed the keeping the ball at the center of his vision should be the goal; hit it and run. Next, we agreed to not even think of the catcher until we swung the bat. And finally, that the infielders, specifically the shortstop and the second baseman, were only to be seen when my son rounded first on his way to second, and then to third and then home.
That level of focus is easy to explain, but hard to put into practice. It took a few games to get this all working. And when it did, not only did my son’s team get more runs and wins, but they beat that same team when they saw them in the playoffs.
“What does this have to do with my business?”
Focus, like in baseball, needs to be practiced in business. While businesses should have goals that involve revenue (after all, you are most likely in business to make money), there are other focuses that your eyes and head need to be glaring over.
This is what we are going to discuss today. We are going to look at 3 areas of your business and business security that you should be focusing on this year. If you want your business to have a safer and happier 2017, and beat your competition, step up the plate!
Your workstation and computer
Business security starts and stops with the technology that we use. And, our workstations are 99% of our work. So it makes sense that they should be as secure as possible.
While our computers are central to how we do business, they are not always the shining example of the most secure areas of our lives.
Tip #1: Log off and shut it down
Having an open terminal is bad…bad, bad, BAD!
While some applications require a different login, a hacker that has physical access to an open terminal can infiltrate those devices. An open terminal with a USB port in plain view is fairly susceptible to a hack.
An open terminal in your business, if someone walks away from it, also violates some regulations and compliance standards. For instance, not locking your devices is violating HIPAA compliance.
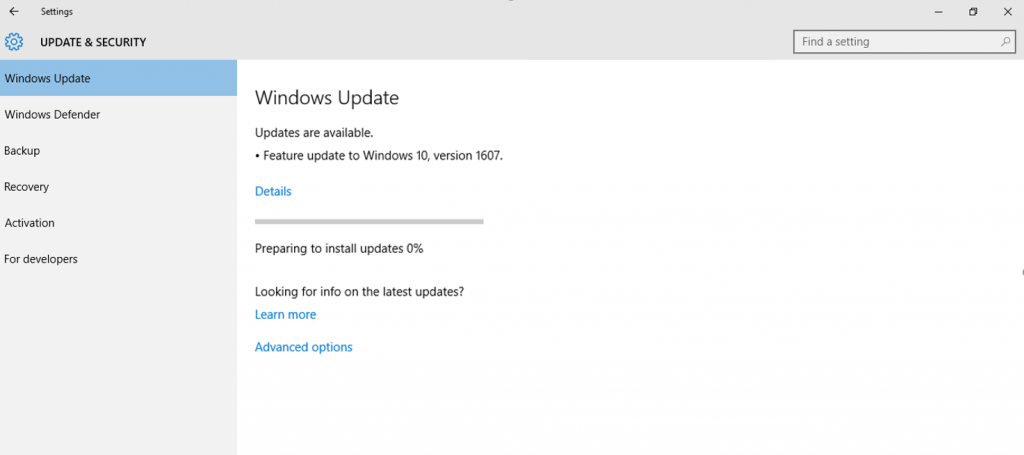
Source: Microsoft
Tip #2: Keep your technology upgraded, updated and current
Basically, all operating system software, anti-virus, business process applications, web browsers and data systems require constant updating and upgrading (where necessary). Not doing so can open you up to larger tiers of violations and fines with compliance agencies.
Air gapping (the physical disconnection of a computing device from a network), may not be enough to prevent the need for upgrades and updates to be installed. This is especially true if a device is connected to your business’s private network, but not the outside internet.

Tip #3: Never, ever use public WiFi on a business device
If your business security is valuable to you, never use an open WiFi with your business laptop, tablet or even mobile phone. The levels of security are so lax on these systems. The networks are heavily trafficked, and no one can accurately conduct security audits for public users in real-time to prevent your device from being a victim.
Because of this, be prepared to have a separate, personal device for your home and non-business use. Business trip? You need to provide your own tablet or laptop and phone. Out for an evening? That phone you are accessing your Facebook account with needs to be a non-business device.
Tip #4: Protect physical workstations with cable locks and more
Software isn’t the only piece of securing your workstation. Encryption and hashing are one thing. But a diligent hacker that gets their hands on a physical piece of hardware only needs time to break into the device.
The most simple method of securing a workstation in physical form is with a cable lock. The FCC recommends cable locks, and HealthIT recommends physical locking as well.
Start with the device; locking, preventing access and controlling use. Then secure the room from traffic and people. From there, secure the floor, then the building. User access and tampering can be as much as a security issue as hacking a password.
Also, as one last piece of physical security for workstations and servers, don’t neglect environmental issues. Do you have adequate ventilation? Are you using fire suppression that is reviewed and tested monthly? Are you elevating servers and workstations to prevent flooding issues?
The data that you share
Data in 2017 is more powerful than currencies and commodities. In fact, digitally, we conduct more financial business on Earth trading cash hand-in-hand each day.
It is something like this…
Well, not entirely like this – we’re not on a roof-top with guns in our hands.
However, there is a need for secure and encrypted method of sharing and storing data. We cannot argue size limits, nor bandwidth limits when it comes to security anymore. Most bottlenecks are slowly lifting, and an image that is only 250 kilobytes needs the same security as a 2 terabyte file.
Tip #1: Use HTTPS connections
A decade or so ago, HTTPS connections were extremely slow. And, unless you were processing financial data (making a purchase, updating bookkeeping, etc), most businesses did not see the need. Today, google Search actually penalizes your rankings because you are not using HTTPS. The technology has sped up and has become even more secure.
There is also a group that is focused on every website using HTTPS connections. To the point that they provide them for free. To be the most secure, you will want to purchase an secure certificate that fits your business needs. But for a basic website that need to securely transmit to and from an end user, it doesn’t get much better than Let’s Encrypt.
Tip #2: Public services, while secure, might not be full compliant
Are you using Google Drive for file storage? Using Google for data processing and sharing for your business? What about Microsoft Outlook? Something like Outlook 365?
Believe it or not, these services are not 100% compliant with many regulations. You can become compliant. Go ahead and review compliance issues for Outlook 365.
One issue that is distressing to many businesses, is that Google services do not have a proper audit trail. This makes them non-compliant with HIPAA needs.

Tip #3: Secure data sharing can be done via SaaS solutions
Why should you choose a secure file sharing solution over the above mentioned? Is a SaaS solution better for your security than simply using encrypted email and secure-FTP?
Most secure business file sharing services fill in those gaps that make email data collaboration and FTP terrible.
PerfectShare is a great example of bypassing those insecure practices and then filling in the compliance and regulations that your business needs. At PerfectShare, we have a focus on correct and real-time reporting, activity tracking and auditing. We also take a secure approach to file storage and file uploads and downloads. Our file sharing action also allows you to remove or use file names and user names in notifications, as some compliance regulations do not allow this data.
We also have other features that help your brand. We use access controls for not only file by file needs, but also on folders. By allowing for archival notices, file and folder tracking and more, we allow your brand to gain more compliance checkboxes filled for your business.
Your passwords and login details
Password security shouldn’t be a last thought when you create your security policy for your business. In fact, passwords should be a first consideration, since they are method we use to wall off potential saboteurs from our systems.
However, in 2017, we are still viewing passwords, as a society, as required, but not as important, until we get hacked. People are still using 123456 as corporate login passwords. You might be using, or know someone that uses, password as their password for their bank’s login.
Don’t neglect your business password security any longer. If you do, you could be one of the thousands that face the $2 million mistake of neglect.
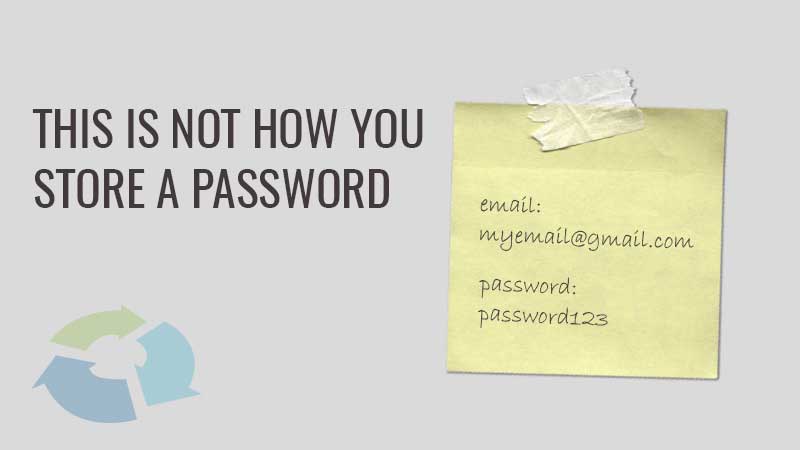
Tip #1: Post-It notes and passwords don’t mix
Password security is aided with longer and longer passwords that are generated randomly. If you are allowed to specify your own password, you can be biased.
What about when the password is “too secure”? Meaning it is either too long, or uses too many special characters, then people forget them. They want quick-fixes for using passwords. Enter sticky notes?
Writing down your password and sticking it to your monitor amounts to you pre-filling every business password you have. It allows for someone to simply take the sticky note, and login, destroy and get away with it.
Instead, use a password manager. Not only can these save your passwords, but they can save them and retrieve them cross-platform and cross-device. They are enabled with random password generators as well. And, most important, they are fully encrypted.
Tip #2: One password for every login is dumb security
Isn’t it great when you remember a long, secure password? So, what’s the issue? You start using that email + password combination for each and every login.
One password with one email address for every single login is just as insecure as shouting out your password for a specific login. Once someone finds out your most used password, it gets tried everywhere. This is how your LinkedIn gets hacked. And that is how your Facebook gets hacked. Then what? Then your bank account, database, web hosting service and more all become hacked.
Use one password for each login needed. This, in conjunction with a password manager, allows your logins to be nearly 100% secure.
Tip #3: Easily remembered passwords = easily hacked passwords
123456, password and qwerty are easily remembered. This means that they are BAD for security. Any password or login details that are easily remembered, are easily guessed – and that is a no-no.
Instead, you need to use random password generators for your passwords. You can find basic password generators at Dashlane.com, Random.ORG or Last Pass. These are websites that allow you to alter settings to get a computer generated random password.
for additional security, you can also use the random password generator function in your password manager. Most common brands have passwords that are both random and strong for any business need.